We’re going to keep the pattern going and attack another free Sherlock from HackTheBox called Origins. This is rated “Very Easy” and just consists of a .zip file download containing a .pcap file. As is customary, the password to extract the files is hacktheblue.
We’re going to keep the pattern going and attack another free Sherlock from HackTheBox called Origins. This is rated “Very Easy” and just consists of a .zip file download containing a .pcap file. As is customary, the password to extract the files is hacktheblue.
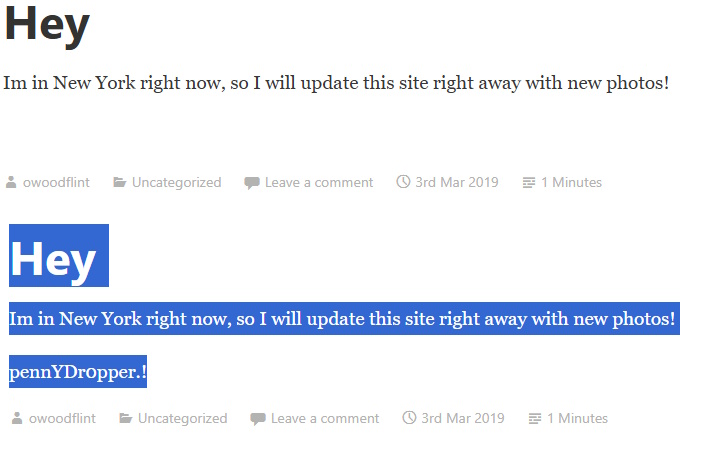
Here’s our scenario for this adventure:
A major incident has recently occurred at Forela. Approximately 20 GB of data were stolen from internal s3 buckets and the attackers are now extorting Forela. During the root cause analysis, an FTP server was suspected to be the source of the attack. It was found that this server was also compromised and some data was stolen, leading to further compromises throughout the environment. You are provided with a minimal PCAP file. Your goal is to find evidence of brute force and data exfiltration.
Since our only evidence is in a .pcap file, we’ll have to fire up Wireshark (or your network traffic analyzer of choice).
Task 1: What is the attacker’s IP address?
Looking in the ftp.pcap file, we have multiple protocols represented. Since we know that the ultimate compromise came from FTP, let’s start by filtering traffic that is using the FTP protocol. Adding this as a filter will do the trick: _ws.col.protocol == “FTP”. That gets us down to 163 packets out of the 547 in the file. We can see over and over again that the main source making the requests is 15.206.185.207. If you look, the first few entries have a source of 172.31.45.144, but that is responding. The one making the request for the admin user is 15.206.185.207. Then 172.31.45.144 asks for the password. This makes it definitive which side is which.
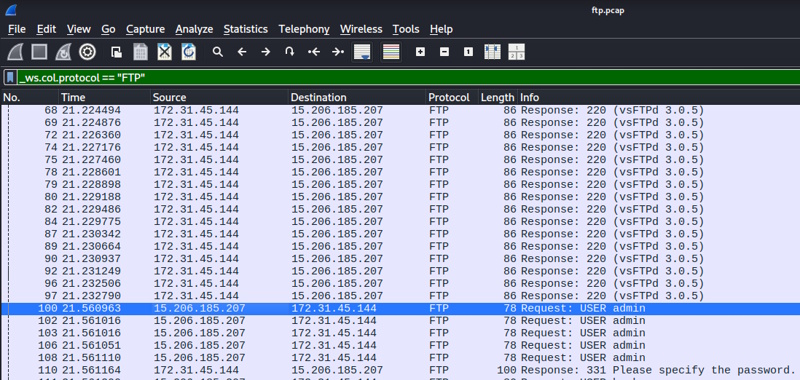
Task 1 Answer: 15.206.185.207
Task 2: It’s critical to get more knowledge about the attackers, even if it’s low fidelity. Using the geolocation data of the IP address used by the attackers, what city do they belong to?
You can go to many different places for this. I’m getting this lookup from this site. Just search the IP and get the city.
Task 2 Answer: Mumbai
Task 3: Which FTP application was used by the backup server? Enter the full name and version. (Format: Name Version)
Take a look back at the filtered capture from Task 1. You can see what the server (172.31.45.144) is responding.
Task 3 Answer: vsFTPd 3.0.5
Task 4: The attacker has started a brute force attack on the server. When did this attack start?
Let’s do an additional filter for only traffic with this IP as the source within the FTP traffic. We can definitely see a brute force attempt happening. If we click the first one (packet 100), it will show details in the bottom left pane. If we expand the Frame 100 section, we can see Arrival Time, UTC Arrival Time, and Epoch Arrival time. The format for the HTB answer wanted one of the two “normal” dates (and not the epoch time). I guessed they wanted UTC as my first shot as that is pretty standard, and that was it.
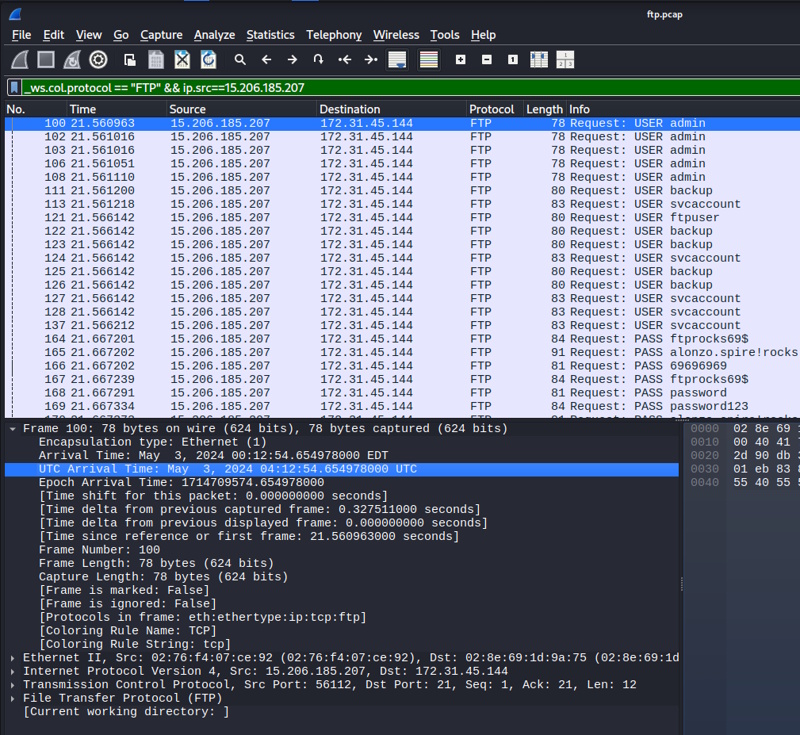
Task 4 Answer: 2024-05-03 04:12:54
Task 5: What are the correct credentials that gave the attacker access? (Format username:password)
For this one, I just scrolled down to the end of the attack. I figured the attack would stop when he was successful. When I got to the last row that had PASS in it (number 407). I then right clicked on it and chose Follow -> TCP Stream Ctrl+Alt+Shift+T. That brings up the entire “conversation” in a window and also adds a filter tcp.stream eq 33 so that you now can see all of the individual pieces that make up what has been assembled for us. But from here, we can see what worked.
220 (vsFTPd 3.0.5) USER forela-ftp 331 Please specify the password. PASS ftprocks69$ 230 Login successful. SYST 215 UNIX Type: L8 FEAT 211-Features: EPRT EPSV MDTM PASV REST STREAM SIZE TVFS 211 End EPSV 229 Entering Extended Passive Mode (|||63192|) LIST 150 Here comes the directory listing. 226 Directory send OK. EPSV 229 Entering Extended Passive Mode (|||40790|) NLST 150 Here comes the directory listing. 226 Directory send OK. TYPE I 200 Switching to Binary mode. SIZE Maintenance-Notice.pdf 213 27855 EPSV 229 Entering Extended Passive Mode (|||9759|) RETR Maintenance-Notice.pdf 150 Opening BINARY mode data connection for Maintenance-Notice.pdf (27855 bytes). 226 Transfer complete. MDTM Maintenance-Notice.pdf 213 20240503034329 SIZE s3_buckets.txt 213 268 EPSV 229 Entering Extended Passive Mode (|||23530|) RETR s3_buckets.txt 150 Opening BINARY mode data connection for s3_buckets.txt (268 bytes). 226 Transfer complete. MDTM s3_buckets.txt 213 20240503034852 EPSV 229 Entering Extended Passive Mode (|||15028|) STOR /home/cyberjunkieX0X/HACKED.txt 550 Permission denied. QUIT 221 Goodbye.
Task 5 Answer: forela-ftp:ftprocks69$
Task 6: The attacker has exfiltrated files from the server. What is the FTP command used to download the remote files?
Look at the command listing from Task 5. You can see it there.
Task 6 Answer: RETR
Task 7: Attackers were able to compromise the credentials of a backup SSH server. What is the password for this SSH server?
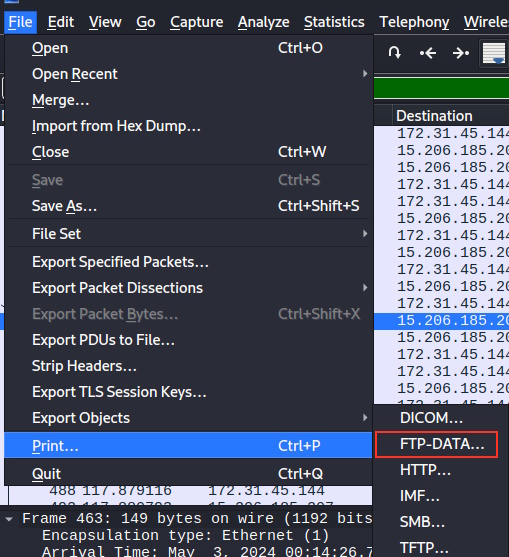
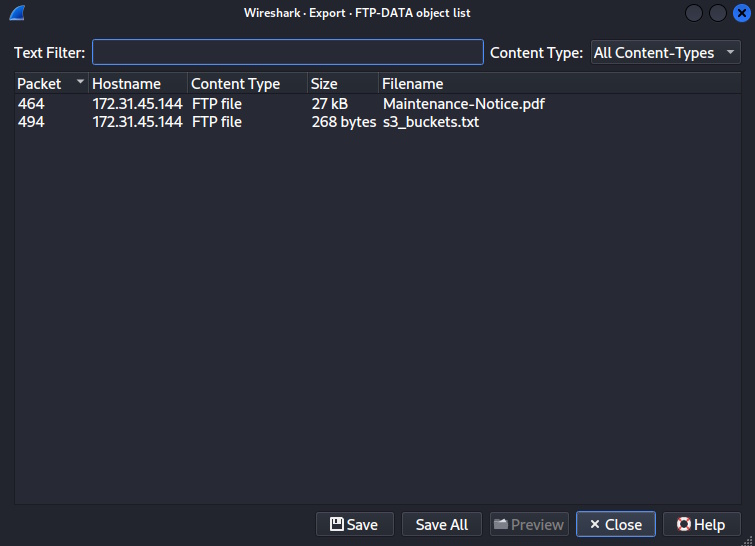
Looking at the conversation in Task 5, I don’t see any passwords directly compromised during that interaction. My guess is that they were in some of the files. Let’s take a look at the files that were downloaded. We can see that it looks like the attacker got a file called Maintenance-Notice.pdf and one called s3_buckets.txt. Let’s just go up to the File Menu and select Export Objects -> FTP-DATA. We can then choose Save All and put those files in the directory of our choosing.
s3_buckets.txt just contains this
https://2023-coldstorage.s3.amazonaws.com # bulk data from 2023, if required anything from here contact simon or alonzo. Retention period is 4 years https://2022-warmstor.s3.amazonaws.com # pending audit, email alonzo at archivebackups@forela.co.uk for any clearance
Maintenance-Notice.pdf has a lot of information, but contains this juicy paragraph:
For team members requiring urgent access to the backup SSH servers during the maintenance period, you can use the temporary password "**B@ckup2024!**" - kindly ensure this information is handled securely and do not share it outside of our team.
Task 7 Answer: **B@ckup2024!**
Task 8: What is the s3 bucket URL for the data archive from 2023?
Just check up in the contents of s3_buckets.txt.
Task 8 Answer: https://2023-coldstorage.s3.amazonaws.com
Task 9: The scope of the incident is huge as Forela’s s3 buckets were also compromised and several GB of data were stolen and leaked. It was also discovered that the attackers used social engineering to gain access to sensitive data and extort it. What is the internal email address used by the attacker in the phishing email to gain access to sensitive data stored on s3 buckets?
This is also in the s3_buckets.txt file.
Task 9 Answer: archivebackups@forela.co.uk
And there we go. That was a fun little exploration of some of the things that Wireshark can do for us.
 Today I’m going to be doing another free Sherlock from Hack the Box called
Today I’m going to be doing another free Sherlock from Hack the Box called 
 Our capture the flag walkthrough today is found over on Hack the Box (HTB). Instead of the offensive security walkthroughs that I’ve been doing, this one is more focused on defensive investigative skills. These classifications for these rooms at HTB are called “Sherlocks” and today’s room is a retired free one called
Our capture the flag walkthrough today is found over on Hack the Box (HTB). Instead of the offensive security walkthroughs that I’ve been doing, this one is more focused on defensive investigative skills. These classifications for these rooms at HTB are called “Sherlocks” and today’s room is a retired free one called 

 Today’s room is called
Today’s room is called