![]() This time, we’re going to be back in a Hack the Box challenge called The Puppet Master. Its description is “An anonymous source has shared a photograph of an unidentified military armored vehicle during field operations. Your mission is to conduct a comprehensive OSINT analysis to identify this vehicle and its specifications.”
This time, we’re going to be back in a Hack the Box challenge called The Puppet Master. Its description is “An anonymous source has shared a photograph of an unidentified military armored vehicle during field operations. Your mission is to conduct a comprehensive OSINT analysis to identify this vehicle and its specifications.”
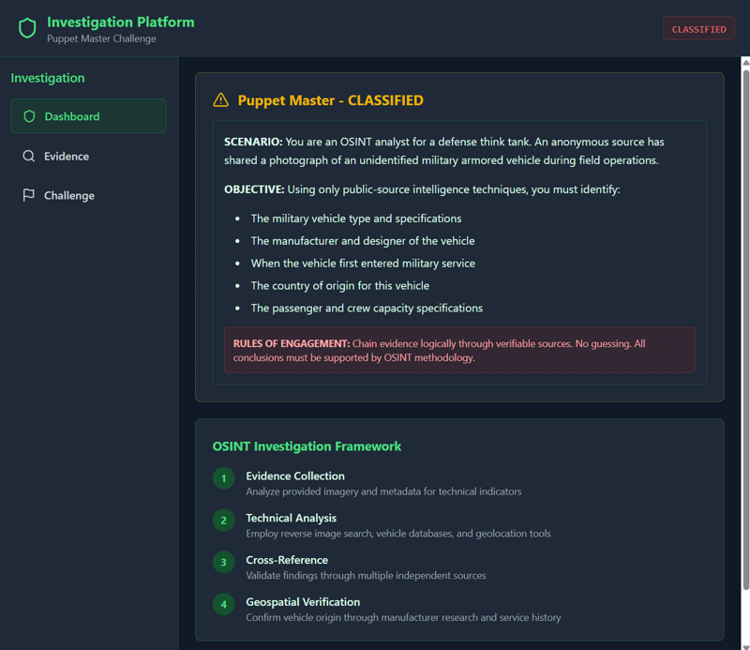
The first thing you have to do is click “Start Instance” on the HTB page for this challenge. It will spin up a container and you’ll get an IP and Port to connect to. When you get there, you will get a website with these pages.
First, we come to the Dashboard page. This explains the Scenario, the Objective, and some information about OSINT Investigation as a whole.
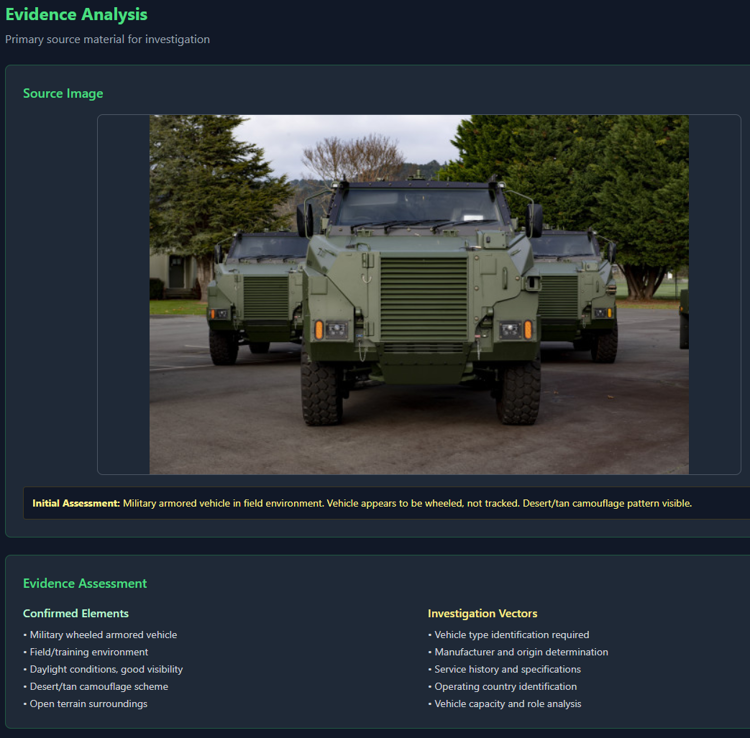
Next, we come to the Evidence page. This has the image for us to investigate and some initial observations about that image.
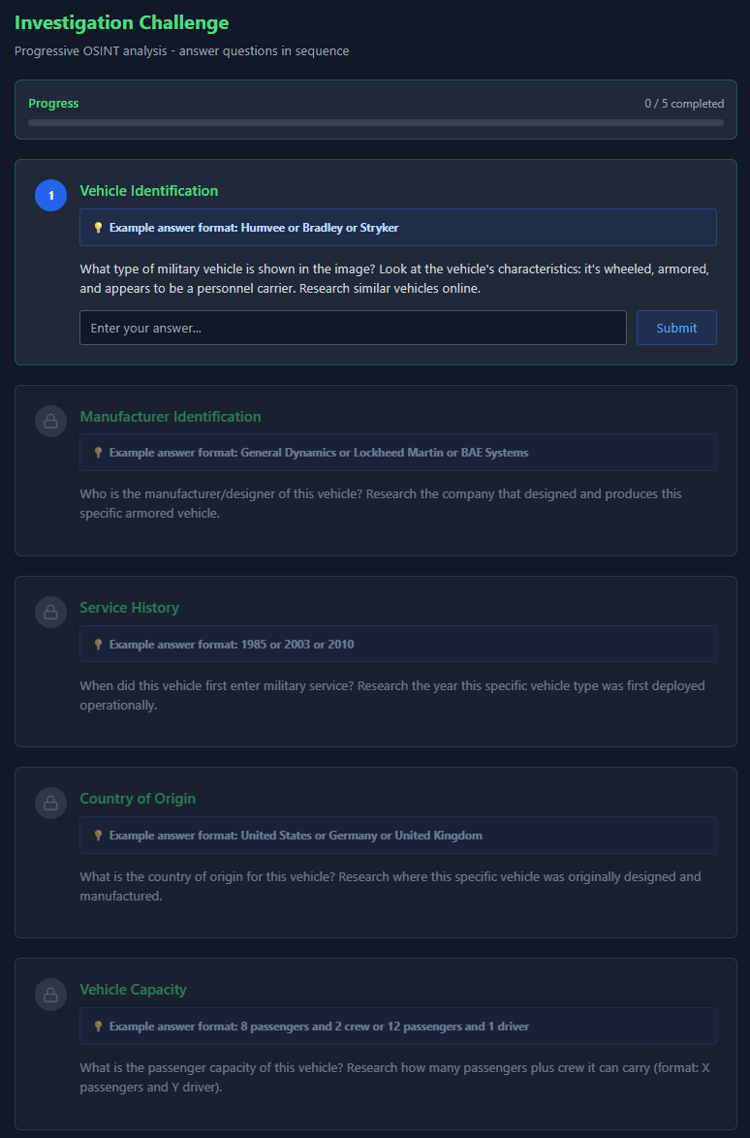
Lastly, we have the Challenge page. This is the page with the list of questions that we will need to answer.
Now that we’ve got the lay of the land, let’s tackle the questions.
Q1. What type of military vehicle is shown in the image? Look at the vehicle’s characteristics: it’s wheeled, armored, and appears to be a personnel carrier. Research similar vehicles online.
I went to tineye.com and uploaded the image. I purposely didn’t select any pages that looked like they were related to solving this challenge. I went to this blog: https://defense-studies.blogspot.com/2023/05/ and found an article mentioning that 18 Bushmaster PMVs were delivered to the New Zealand Army.
A1. Bushmaster
Q2. Who is the manufacturer/designer of this vehicle? Research the company that designed and produces this specific armored vehicle.
I googled it and was pointed to the Wikipedia article for it and got the answer https://en.wikipedia.org/wiki/Bushmaster_Protected_Mobility_Vehicle
A2. Thales Australia
Q3. When did this vehicle first enter military service? Research the year this specific vehicle type was first deployed operationally.
Same wikipedia page
A3.1997
Q4. What is the country of origin for this vehicle? Research where this specific vehicle was originally designed and manufactured.
Same page, though the name of the manufacturer is also a bit of a giveaway
A4. Australia
Q5. What is the passenger capacity of this vehicle? Research how many passengers plus crew it can carry (format: X passengers and Y driver).
Wikipedia page again.
A5. 9 passengers and 1 driver
After you finish that last question, you submit for final analysis and get the flag to submit back at the Hack the Box Challenge page. That’s it. Very Easy as the chaps promised. The biggest trick here was knowing how to use TinEye or Google Reverse Image Search and then to investigate from there.
 Today’s room is called
Today’s room is called